Analyzing the Hidden Hazard of Atmosphere Variables for Protecting Secrets and techniques
Cloud
Whereas DevOps practitioners use setting variables to recurrently maintain secrets and techniques in purposes, these could possibly be conveniently abused by cybercriminals for his or her malicious actions, as our evaluation exhibits.
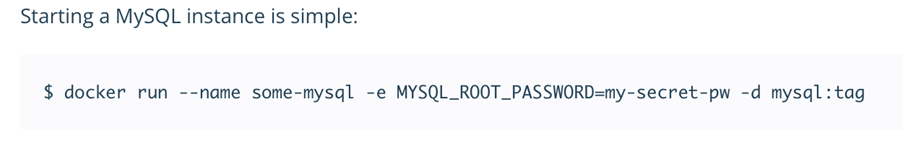
The usage of setting variables is a standard observe within the DevOps group because it offers easy accessibility to configuration properties. It turns out to be useful particularly inside containerized environments: It’s extra handy to move configuration as an setting variable. Nevertheless, from a cloud security perspective, passing a secret inside an setting variable ought to be averted and mentioned extra. It’s because this observe is straightforward to implement and it could be dangerous if any confidential data is saved inside, leaked, and/or abused for a couple of occasion of compromise.
What are setting variables?
Atmosphere variables are a set of key-pairs legitimate for an setting — sometimes a shell or a subshell. These key-pairs will be outlined in varied methods, with one of many world definitions being export command. This command is often used inside shell scripts, when utilizing the -e parameter when beginning containerized purposes on a Linux working system, or when used earlier than a container construct the place the command ENV on a Dockerfile signifies that the variable can be set on runtime. Atmosphere variables aren’t encrypted and can be found in plain textual content throughout the scope of the setting.
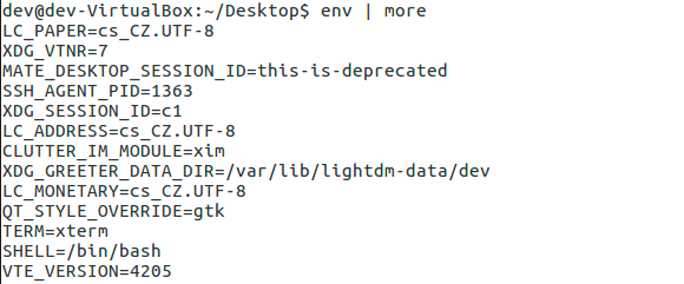
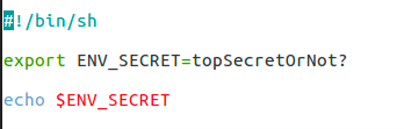
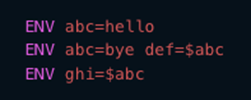
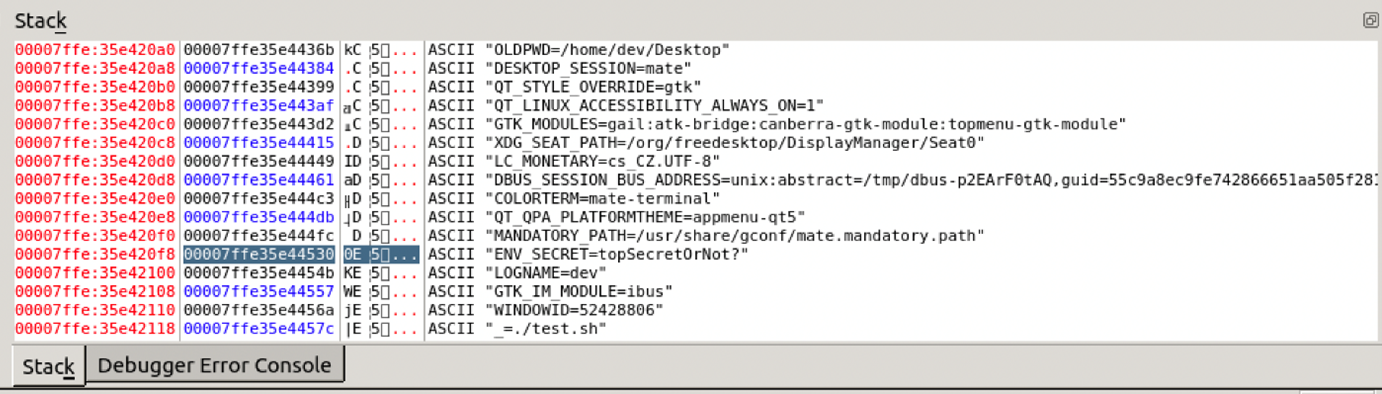
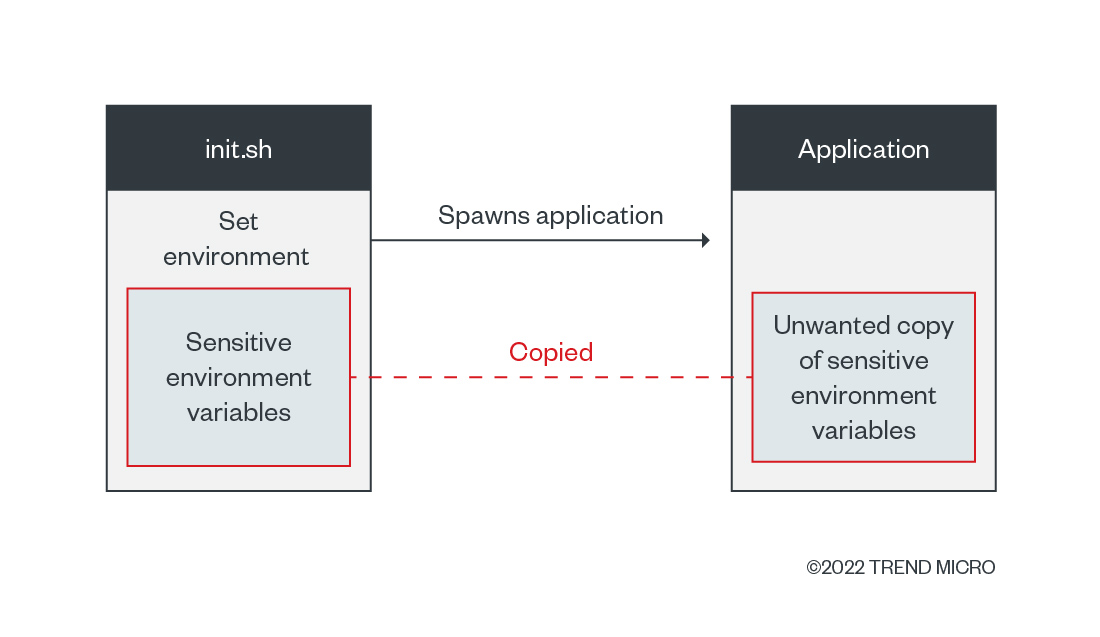
What does all these definitions imply technically? We have to outline the scope validity of setting variables. In conditions just like the one proven in Determine 2, the scope is certain by the shell script or executing setting and its baby processes. When containers are used, the boundary is about by the container course of and its baby processes. These properties indicate that the variables are copied inside each baby course of.
By analyzing the technical particulars, we discover that variables are copied to a stack of working processes which are subsequently copied to spawn baby processes. This element implies that the variables may even be copied into this new course of if a developer is:
- Executing a wrapper utility; or
- Beginning a script that makes use of setting variables for configuration and beginning different purposes that don’t essentially want these configuration fields.
Why is using setting variables dangerous for secrets and techniques?
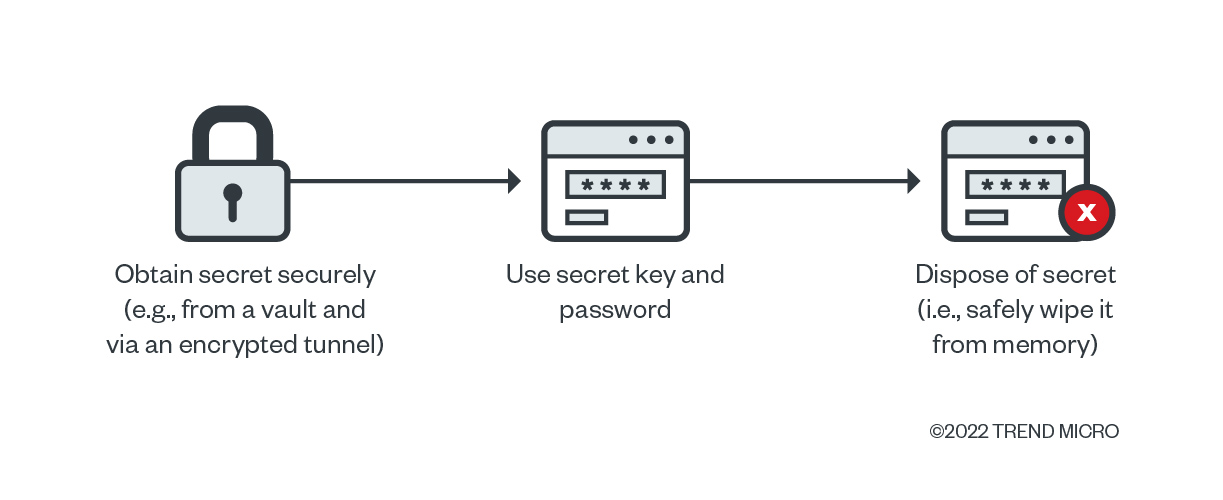
We beforehand published an article on the significance of correct secrets and techniques administration, how improper practices might enable entry to essential programs, and the way the leakage of secrets and techniques might finally result in supply-chain compromise. However what is taken into account the perfect secrets and techniques administration observe? We’ve got mentioned and enumerated the next suggestions:
- Encrypted storage: Retailer credentials and secrets and techniques with one other password.
- Transport utilizing safe channels: Configure the channels used to maneuver and switch secrets and techniques to be protected from interception and leakage.
- Common secrets and techniques rotation: Outline a daily interval for updating the credentials within the database or service.
- Quick availability: In precept, a secret ought to be current within the reminiscence for a restricted time. As soon as it’s used, delete the reminiscence area.
If we agree that these 4 factors have a major affect on secrets and techniques safety, then using setting variables violate the fourth level, “Quick availability,” by its definition. Quick availability by itself implies that a secret is current contained in the reminiscence quickly and is eliminated upon its utilization. We are able to relate this method to working system implementations, successfully stopping the secrets and techniques from being discovered inside one other course of as a part of uninitialized reminiscence.
How dangerous can it’s?
For example, we analyzed the setting itself whereas working a MySQL database inside a container and located that the leakage of an setting variable storing a root password can assume a extra significant issue, in comparison with accessing the key itself (that’s, the foundation password).
Nevertheless, when executing serverless features (by way of an occasion or set off similar to accessing the endpoint, database, or message queue) contained in the default service of a cloud service supplier (CSP) and containing delicate setting variables, the execution itself might result in a full-service compromise or distant code execution (RCE) based mostly on a reminiscence learn vulnerability. As we published before, the impression could possibly be dangerous as if the consumer have been offering the code to be executed.
The hidden hazard of utilizing setting variables for secrets and techniques administration is that the architectural resolution might enable customers to unwillingly cross safety boundaries even with solely a single piece of knowledge leaked. The chance of leakage will increase with the copy-and-paste characteristic inside each baby course of, whereby each utility that spawns one other program as a baby course of is extra more likely to be susceptible.
The properties of setting variables could possibly be unknown to DevOps groups when designing their purposes and when a generally used observe is reused (that’s, app builders’ ordinary utilization of utilizing setting variables for storing secrets and techniques). Because of this, builders ought to pay attention to these properties and their programming’s implications when designing their merchandise. The very best case on this situation: avoiding utilization of setting variables for secrets and techniques storage.
Cloud secrets and techniques in setting variables
Whereas researching on cloud providers and monitoring an incident, our group seen some CSPs additionally training this technique for various steps on their authorization protocols. To maintain their providers’ safety, we have now mentioned this concern with the CSPs and opted to not establish these suppliers.
When a developer must run their command-line interface (CLI) instruments, and even extensions for growing on platforms similar to Visible Studio Code, they carry out an preliminary configuration course of. A password or secret is requested to grant entry to CSP providers, and the authorization tokens will be saved in two methods for the validation: by way of a neighborhood file containing the tokens, more often than not in plain textual content, or by way of setting variables.
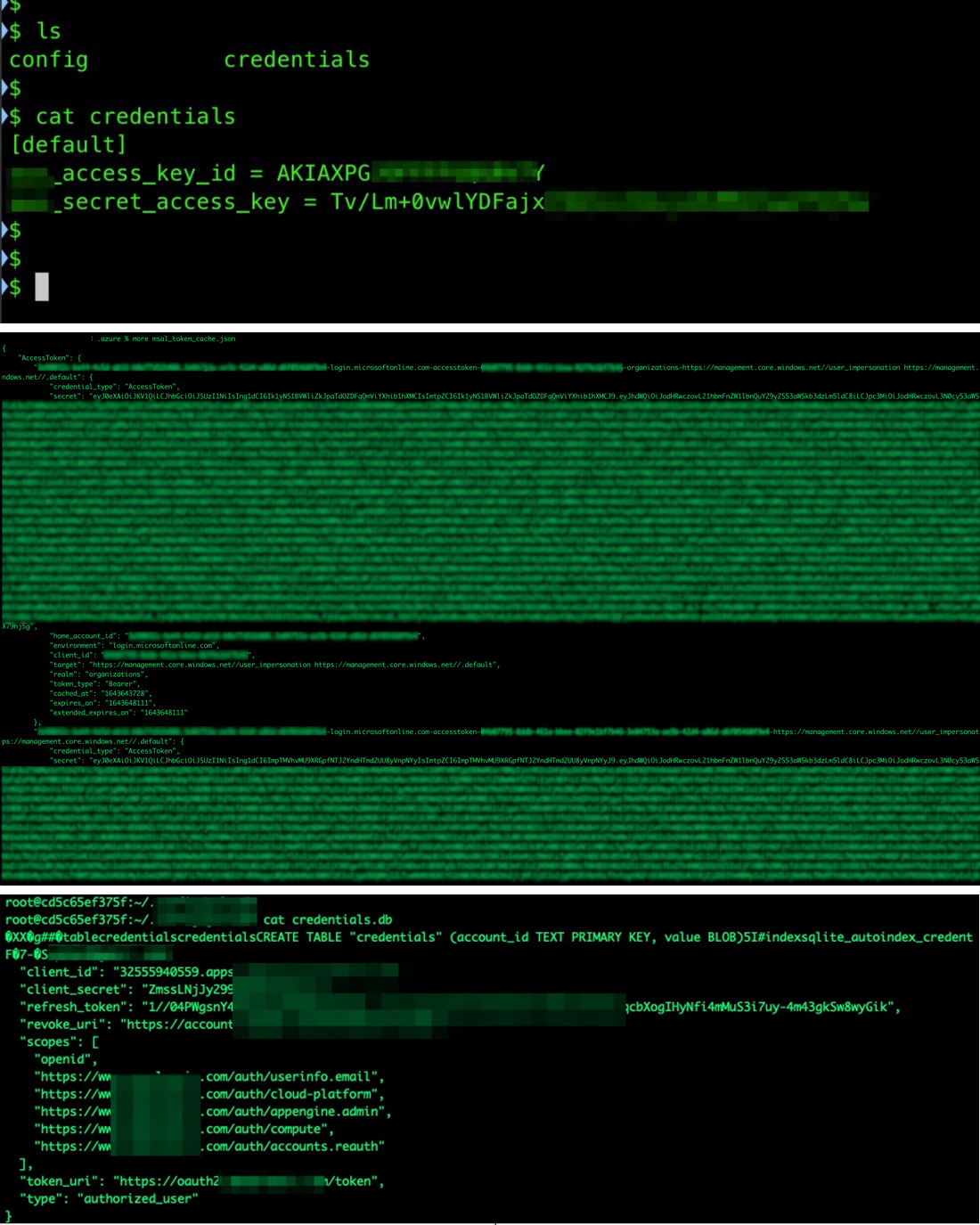
When our group began researching serverless providers, we seen that the identical setting variables on a developer’s machine could possibly be discovered contained in the serverless runtime setting. The secrets and techniques discovered within the setting could possibly be abused in numerous contexts, as we explored and reported in 2019; if an attacker manages to obtain the CSP’s official CLI device contained in the serverless setting, it inherits the authorization and privileges given to the service by way of the secrets and techniques.
Contemplating how straightforward it was to achieve delicate information, we predicted that the cloud, the pipeline, and the instruments would turn into a goal for cybercriminals. We’ve got seen incidents involving some of these compromise in a minimum of two instances. The primary incident noticed the hacking group TeamTNT concentrating on breached cloud environments, particularly on the lookout for delicate setting variables. And extra just lately, reports of a supply-chain assault the place a Python library had its code modified to begin harvesting the identical delicate variable content material.
How prevalent is using setting variables for secrets and techniques?
Seeing as we should not have entry to all supply codes for us to get related data for a radical evaluation, there have solely been estimates reported for the prevalence of this observe. Nevertheless, the mindset that many builders have is that conserving secrets and techniques in setting variables is “the most secure strategy to deal with your secret keys/password,” as exemplified in Determine 9.
We think about using vaults as a greater choice for storing secrets and techniques than setting variables. We additionally recommend acquiring secrets and techniques solely when they’re wanted and solely whereas utilizing a safe and encrypted channel, and safely wiping the reminiscence as soon as the important thing pair is used. Utilizing this method, a secret can be saved inside a single course of contained in the deployed utility and the undesired spreading to its baby processes, which will increase the assault vector related to the dangers of leaking secrets and techniques, can be averted.
Atmosphere variables and vulnerabilities
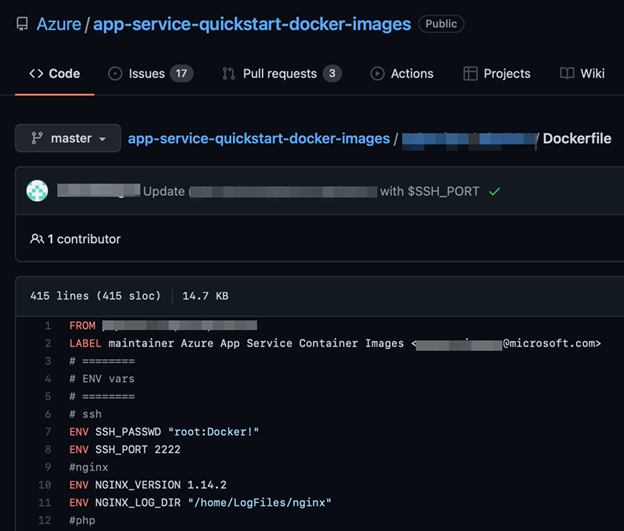
Happily, not everybody considers setting variables the most secure place to retailer secrets and techniques. Nevertheless, in seeing sensible examples whereas researching varied software program merchandise and CSPs, we seen that this downside is downplayed and maybe copied from working with open-source options.
Conclusion
The usage of setting variables for application-related features and information is inherently protected, quick, and environment friendly for growth and deployment. Nevertheless, the saved information mustn’t embrace delicate data or secrets and techniques that could possibly be used for assaults similar to credentials, entry tokens, login URLs, and connection strings. Whereas the DevOps group considers this a standard observe, incidents prior to now have proven that, from a safety perspective, this observe could possibly be abused and have an effect on organizations in the long term.
We emphasize that builders ought to perceive the implications of utilizing setting variables for secrets and techniques administration. We’ve got additionally mentioned safer procedures and proposals for doing so in earlier articles:
The very best-case situation is to keep away from storing secrets and techniques in setting variables utterly as doing so results in extra assault vectors in sure purposes. There are safer methods to handle secrets and techniques no matter how massive the venture or the group dealing with the venture is. DevOps practitioners and builders also needs to needless to say whereas it’s nearly unimaginable to realize a totally safe system, there are instruments to cut back the dangers to a minimal and never present cybercriminals extra assault vectors in purposes. Safety finest practices similar to the next might help mitigate the impression of those dangers:
- Observe CSPs’ suggestions (normally discovered of their respective documentations) for securing environments and initiatives.
- Use vaults to retailer keys and passwords. This will likely incur extra prices to the group or group, but it surely provides customers and safety groups a further layer of safety for his or her credentials’ storage.
- Use customized photos. Whereas default providers enable for velocity and effectivity for deployment and growth, customized container picture designs and implementations give builders extra room for out-of-the-box options and extra safety.
- Use encrypted channels and pipelines. Locking the values of the variables ensures that delicate data similar to passwords and IDs stays secret in situations of unauthorized entry.
Tags
sXpIBdPeKzI9PC2p0SWMpUSM2NSxWzPyXTMLlbXmYa0R20xk
Source link
